“If you’ve been playing the ukulele for a while and you’re starting to get tired of the “same old, same old” but don’t know where to turn, Clawhammer could be just the thing to kick-start your strumming. It worked for me”
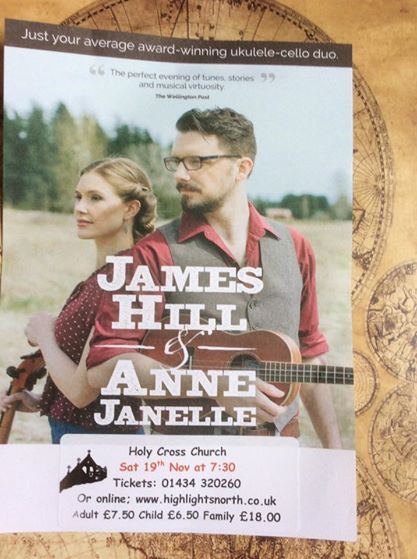
James Hill
Ukulele Yes!
The Ukulele Teacher’s eZine
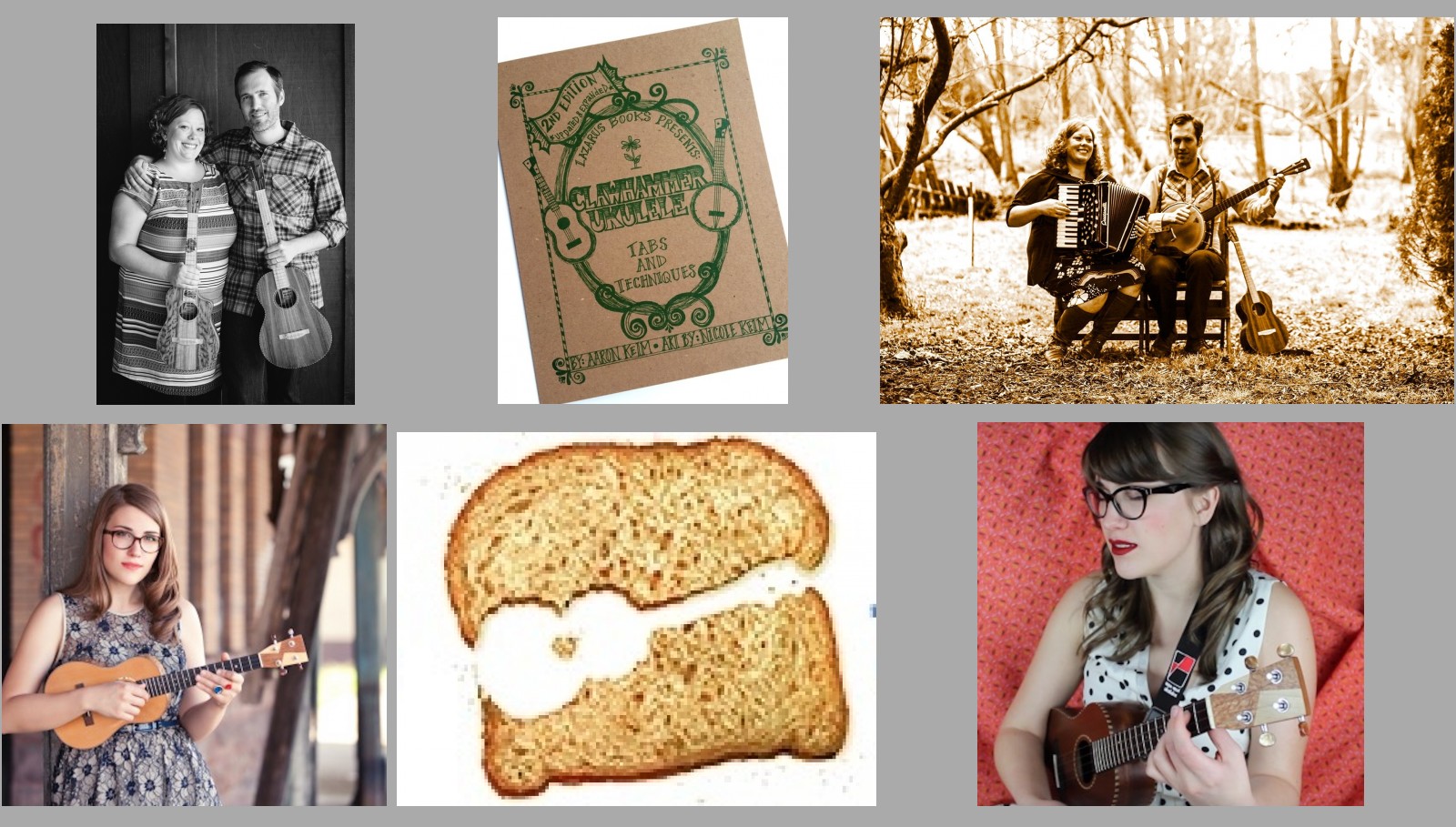
Clawhammer Ukulele Workshop
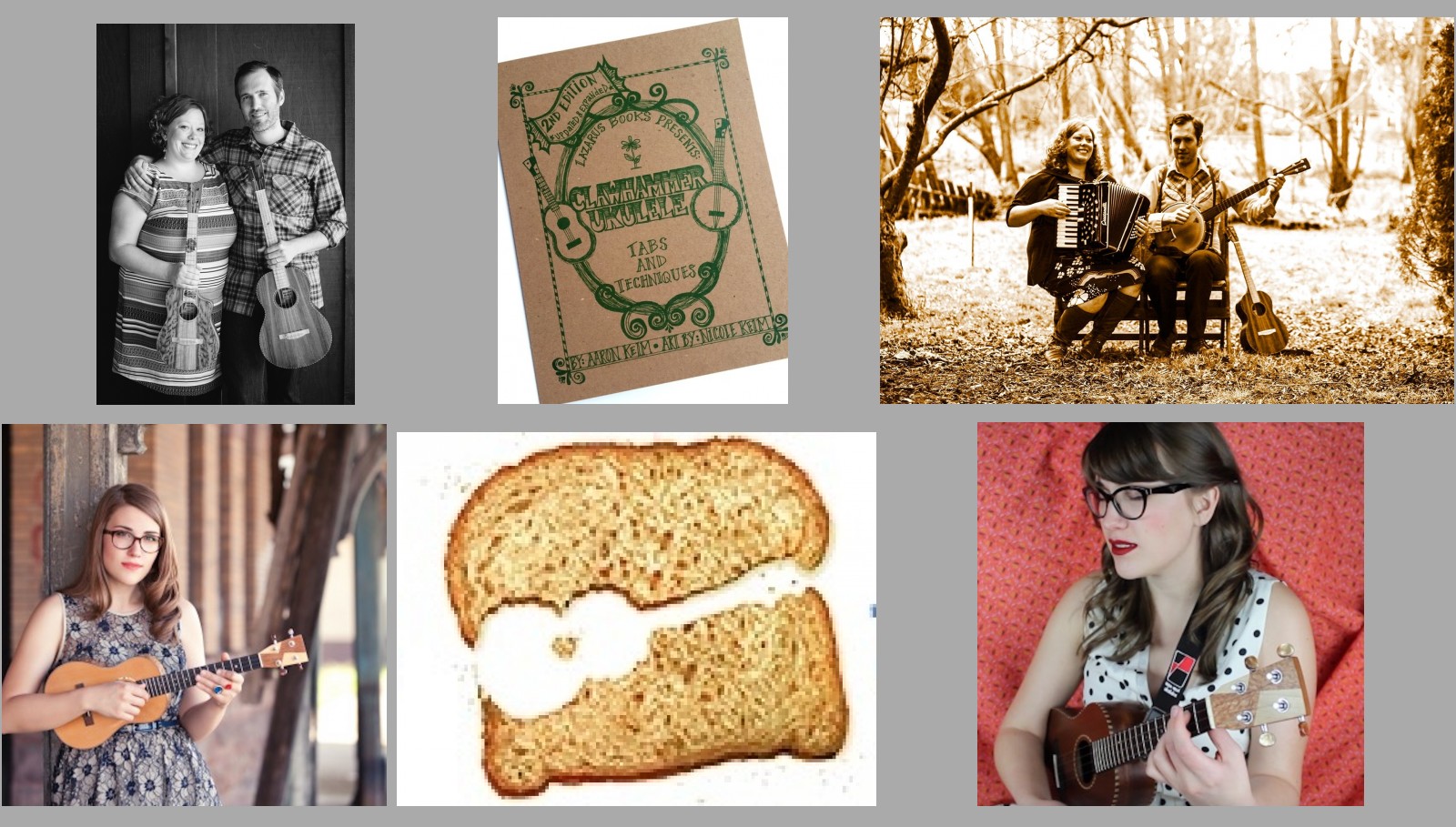
Aaron Keim
Plus Concert!
“The Quiet American”
and joining them onstage as their Special Guest
“Danielle Ate The Sandwich”
Wed 25 May 2016
The Cumberland Arms
Newcastle upon Tyne NE6 1LD
WORKSHOP: 6:50 – 7:50 (Doors 6:30)
(Max attendance: 30)
CONCERT: 8:20 – 9:45 (Doors 8:00)
(Max attendance: 50)
RAFFLE: 9:45 – 10:00
As well as Super Surprise Prizes donated by
The Quiet American and Danielle Ate the Sandwich,
many thanks to Ben Rouse for getting us,
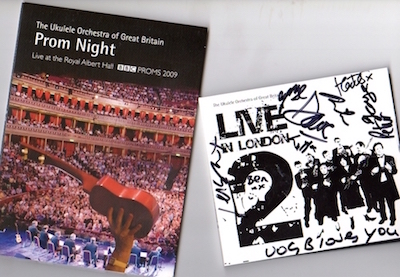
and the Ukulele Orchestra of Great Britain (UOGB) for giving us,
– UOGB Prom Night DVD
– a signed copy of the UOGB “Live in London 2” CD!
Full ticket: £20 (no booking fee)
Concert-only ticket: £5 (no booking fee)
Tickets: If you attend Thursday sessions at The Cumberland or Sunday Sessions at The Millstone, please help to reduce event costs by buying a paper ticket from me, rather than buying online. You can email me to reserve a paper ticket:
Liz Panton: spam-protected email link i…@u…g.uk
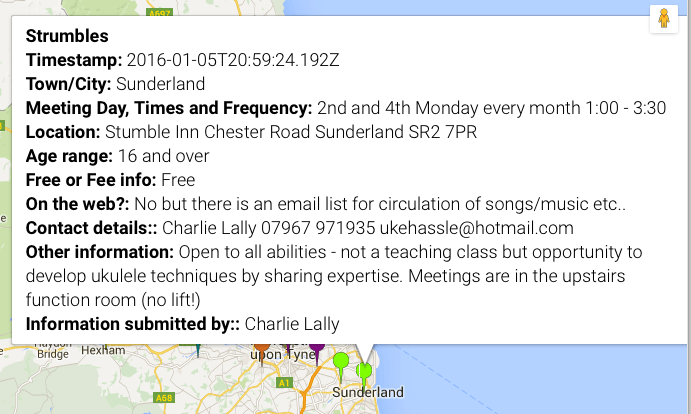
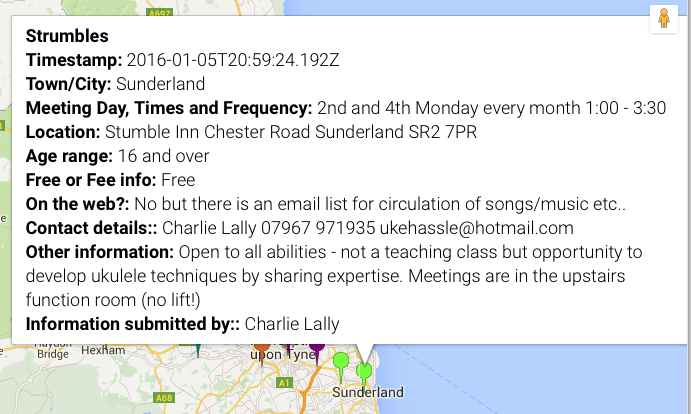
Ukulele players:
Clawhammer works best with a high G string. However, if you only have a low G uke, it will be fine for the workshop.
Baritone ukulele players:
If you are bringing a Baritone ukulele you will also need to bring a capo!
Ukulele Hunt article: Ukulele capos: what to get
More workshop and concert details plus link to online ticket sales:
http://eepurl.com/bZQXQn
This event is also on Facebook – please share with your friends! Facebook Event

Many thanks to the Grand Northern Ukulele Festival for organising and sponsoring this fantastic UK Tour by
Aaron and Nicole Keim and Danielle Anderson!

Home